State-linked hackers tracked as Silk Typhoon have been observed hijacking network captive portals to redirect diplomats to a malware-serving site, Google Threat Intelligence Group (GTIG) reports. The operation used an advanced adversary-in-the-middle (AitM) technique to intercept Chrome’s captive-portal checks and deliver a multi-stage payload that ultimately installs a PlugX-style backdoor. GTIG attributes the activity to UNC6384 and links it to the Chinese cluster TEMP.Hex (also known as Mustang Panda and Silk Typhoon) based on tooling, targeting, and infrastructure.
How the Captive Portal Hijack Worked
The intrusions relied on intercepting web traffic at the network edge and exploiting how Chrome verifies internet access behind captive portals. When a browser connects to a new network, Chrome issues requests to detect whether a captive portal is present. GTIG found attackers positioned to hijack that flow and redirect users to a malicious landing page posing as an Adobe plugin update site.
On the fake landing page, targets were presented with a digitally signed executable named AdobePlugins.exe and step-by-step instructions meant to coax them into bypassing Windows security prompts during installation. The file displayed a legitimate Microsoft Visual C++ installer UI but then fetched a disguised MSI (file named 20250509.bmp) that contained multiple components:
- A legitimate Canon printer tool
- A DLL loader named CANONSTAGER
- An RC4-encrypted backdoor labeled SOGU.SEC
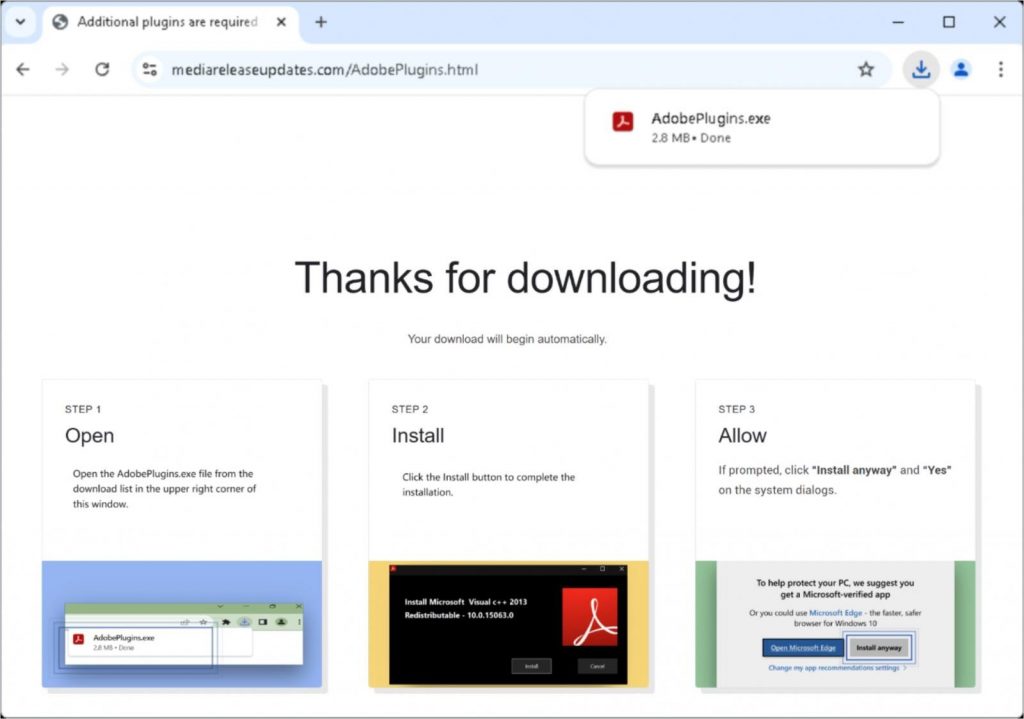
Fake site prompting Adobe plugin installation
Source: Google
CANONSTAGER decrypts the encrypted payload and loads it into memory using DLL side-loading. The final payload, SOGU.SEC, is described by Google as a variant of PlugX, a remote access/espionage tool widely used by Chinese-nexus threat groups. Functionality observed in the samples includes system reconnaissance, file upload/download, and an interactive remote command shell.
Evidence, Edge Compromise Theory, and Open Questions
GTIG researchers consider the AitM feasible if an edge device on the victim network was compromised, but they did not find conclusive proof of that specific compromise. The report details the redirection and the staged download behavior, but the precise initial foothold—whether via an edge appliance exploit, rogue Wi-Fi, or misconfiguration—remains under investigation.
A separate attribution detail that drew attention: the AdobePlugins.exe binaries were digitally signed by Chengdu Nuoxin Times Technology Co., Ltd. GTIG noted at least 25 malware samples signed by this entity since early 2023 that appear linked to Chinese activity clusters. Researchers stopped short of declaring the vendor complicit; instead they raised the possibility the signing credentials were either abused by a threat actor or the supplier was compromised.
GTIG’s guidance in the disclosure includes this observed defensive posture: “Treating all certificates from Chengdu Nuoxin Times Technology Co., Ltd as untrusted is a reasonable defensive action until the situation is clarified.”
Technical Chain: From Browser Check to In-Memory Backdoor
The technical chain observed by GTIG proceeds as follows:
- User connects to a network and Chrome performs a captive-portal check.
- The attacker hijacks the captive-portal redirect and serves a landing page impersonating an Adobe update.
- Victim downloads AdobePlugins.exe (digitally signed) and follows on-screen instructions to bypass security prompts.
- The installer fetches a disguised MSI (
20250509.bmp) that contains a Canon tool, CANONSTAGER, and the RC4-encrypted SOGU.SEC payload. - CANONSTAGER decrypts and side-loads the final payload into memory.
- SOGU.SEC (PlugX variant) executes espionage functions: host profiling, file transfer, and remote command execution.
GTIG highlights the use of DLL side-loading and in-memory execution as techniques aimed at avoiding disk-based detection and improving stealth during post-exploitation.
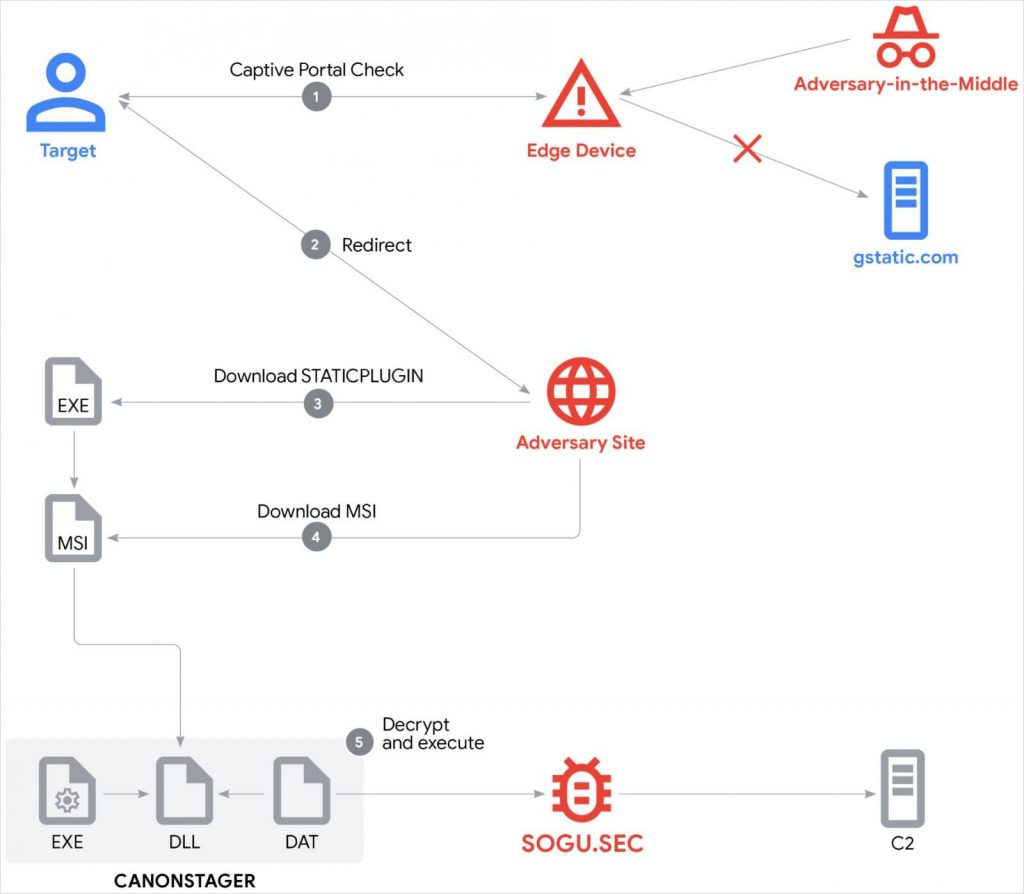
Overview of the attack chain
Source: Google
Google’s Response and Shared Detection Material
As part of its response, Google blocked the malicious domains and file hashes through its Safe Browsing systems and issued government-backed attacker alerts to impacted Gmail and Workspace users. GTIG also provided detection artifacts to defenders: YARA rules for identifying STATICPLUGIN and CANONSTAGER, along with indicators of compromise (IoCs) for all sampled files from the campaign. Those shared rules and IoCs are intended to help network defenders hunt for related activity and block observed payloads and domains.
Targeting, Tradecraft, and Operational Pace
GTIG emphasized the campaign’s targeted nature—diplomats and likely high-value individuals were the intended recipients—and the sophisticated tradecraft: captive-portal AitM, signed binaries, stepwise social engineering on the landing page, encrypted payloads, and in-memory execution.
The observation that a single certificate issuer appears across multiple malicious builds since 2023 suggests either persistent abuse of signing keys or repeated compromise of a signing infrastructure that threat groups can leverage.
GTIG’s broader assessment is consistent with recent trends: Chinese-nexus espionage actors increasingly adopt resilient infrastructure and modular binaries and move rapidly between builds and operational hosts when a TTP or domain is disrupted.
What the Disclosure Means for Organizations
GTIG’s findings show how network-level interception combined with crafted user flows can convert routine browser checks into a malware delivery vector.
The campaign demonstrates a chain where social engineering and trusted UIs (an Adobe update dialog, a signed executable) are used to lower user suspicion while technical layering (DLL side-loading, RC4 encryption) reduces detection signals.
Because the report includes YARA rules and IoCs, enterprise defenders and CERT teams can incorporate those artifacts into hunting and detection pipelines.
Ongoing Investigations and Attribution Nuances
GTIG’s tracking of UNC6384 and mapping to TEMP.Hex / Mustang Panda / Silk Typhoon is based on overlapping infrastructure, tooling, and victimology. As with many nation-linked clusters, attribution remains multifaceted and probabilistic—GTIG links observed code, infrastructure and targeting patterns to the cluster but continues to monitor for changes in tooling and infrastructure that might refine or alter the assessment.
The status of Chengdu Nuoxin Times Technology Co., Ltd’s signing keys and whether the company knowingly signed malicious binaries is part of ongoing inquiry. Until investigators clarify the provenance of those certificates, GTIG’s advisory to treat them cautiously stands as an observed, not prescriptive, data point.
GTIG’s report outlines a focused AitM campaign that hijacked captive-portal flows to deliver a signed dropper that ultimately loads an RC4-encrypted PlugX variant. The operation targeted diplomatic users and combined social engineering, signed binaries, in-memory payloads, and DLL side-loading.
Google mitigated immediate risks by blocking domains and hashes via Safe Browsing and releasing YARA rules and IoCs, while GTIG continues to monitor the cluster they track as UNC6384 / TEMP.Hex.
The campaign underscores how adversaries are evolving delivery chains to exploit trusted user workflows and leverage digital signatures and network-level interception to reach high-value targets.









