Nissan has confirmed a data breach tied to its Tokyo-based design subsidiary, Creative Box Inc. (CBI), after unauthorized access was detected on a CBI server. The Qilin ransomware group says it stole four terabytes of data, including sensitive design assets, and has posted samples on its dark-web site to pressure the automaker.
What Nissan Confirmed About the Intrusion
Nissan says suspicious access was identified on August 16, 2025, on a CBI data server used for design work. According to the company, CBI “immediately implemented emergency measures,” including blocking server access and notifying police. The automaker has verified that “some design data has been leaked” and says a detailed investigation is ongoing. Nissan also clarified that the exposed information concerns Nissan only, as CBI’s sole customer, and does not involve other clients or third parties.
What Qilin Ransomware Claims it Stole and Published
On August 20, 2025, Qilin listed CBI on its extortion portal and claimed to have taken all active design projects. The group says the cache includes 3D vehicle design models, internal reports, financial documents, VR design workflows, and photos. As proof, Qilin published 16 images that appear to show car design renders, spreadsheets, interior visuals, and documents.
Who Creative Box Inc. is and Why its Data Matters
CBI is a wholly owned Nissan design studio established as a think tank for experimental and concept vehicle work. Its environment hosts pre-release design models and workflows that reflect future product directions. Loss or exposure of such intellectual property can reveal styling, component layouts, and research processes that competitors could study.
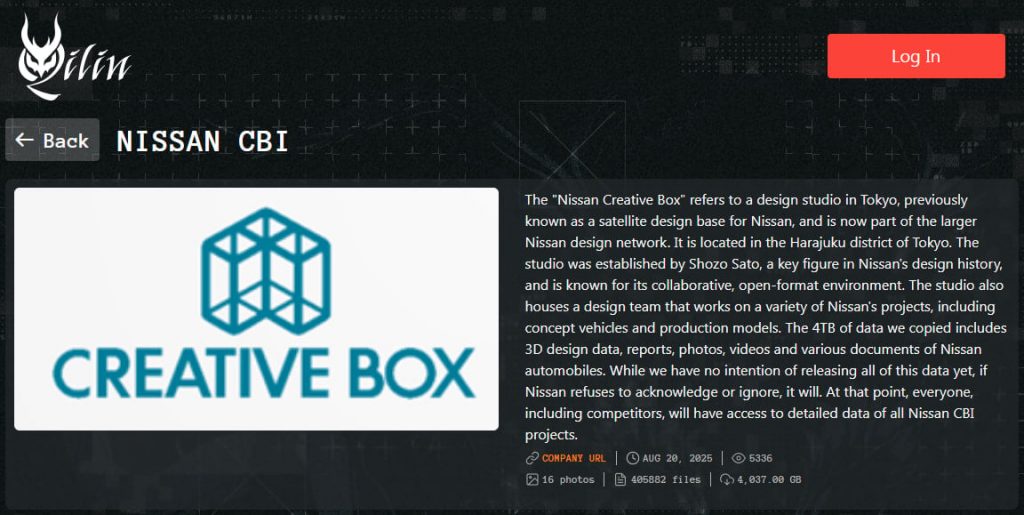
Nissan CBI listed on the Qilin extortion portal
Source: BleepingComputer
The Ransomware Group’s Recent Activity and Known Tactics
Qilin has run a busy campaign this year, claiming attacks against media and life sciences firms. Investigators have linked the group’s operations to exploitation paths that included the Kickidler employee monitoring tool and two Fortinet vulnerabilities (CVE-2024-21762, CVE-2024-55591) that allowed unauthenticated remote code execution. Qilin typically pairs data theft with public shaming on leak sites to increase pressure.
How the Incident Unfolded, Based on Public Statements
- August 16: Suspicious access detected on a CBI data server used for design work.
- Immediate actions: CBI blocks access to the server and reports to law enforcement.
- Verification: Nissan confirms a data breach and that some design data has leaked.
- August 20: Qilin posts CBI to its leak portal, threatening to publish full archives.
What the Exposed Data Appears to Include
The group’s claim centers on confidential design content and supporting business files rather than consumer data. Items cited include:
- 3D vehicle design models and interior renders
- Internal reports and financial documents
- VR design workflows and process materials
- Photos that depict design assets and spreadsheets
Nissan has not provided a public inventory of files, but it acknowledges that design data is among the leaked materials.
Why This Breach Draws Industry Attention
Automotive design pipelines blend CAD assets, VR reviews, and cross-team collaboration. A breach at a specialized design studio like CBI can expose the development rhythm of future programs alongside proprietary methods. Public posting of even partial samples can help rivals infer directionality in materials, ergonomics, and packaging concepts.
Nissan and CBI say the inquiry is ongoing. Key open items include the intrusion path, the scope of exfiltration beyond the samples posted, and whether Qilin retains undisclosed assets. The company says it will “take appropriate measures as needed” as findings develop.