Roku Data Breach has resulted in more than 15,000 Roku accounts sold at a mere 50¢ price. Analysts say there is more to this incident.
The Roku accounts breach occurred when compromised accounts were utilized to make unauthorized purchases of hardware and streaming subscriptions.
However, the repercussions of this attack extend further. Threat actors have been selling the stolen accounts for as little as $0.50 per account, enabling buyers to exploit stored credit card information for illicit purchases.
Company Says 15,363 Roku Accounts Sold in The Breach Using Credential Stuffing
According to the information provided on the Roku website, the company recently disclosed the Roku accounts breach. They have identified that approximately 15,363 customer accounts were impacted by a credential stuffing attack.
What is Credential Stuffing Attack?
In a Credential Stuffing Attack, threat actors collect credentials exposed in previous data breaches and attempt to use them to log in to other sites, in this case, Roku.com.
Roku Accounts Breach Details
The breach allowed the threat actors to modify the account details, including passwords, email addresses, and shipping addresses.
As a result, the legitimate account owners were locked out of their accounts, and the threat actors were able to make purchases using the stored credit card information without the account holders receiving order confirmation emails.
“It appears likely that the same username/password combinations had been used as login information for such third-party services as well as certain individual Roku accounts,”
“As a result, unauthorized actors were able to obtain login information from third-party sources and then use it to access certain individual Roku accounts.”
“After gaining access, they then changed the Roku login information for the affected individual Roku accounts, and, in a limited number of cases, attempted to purchase streaming subscriptions.
Reads the data breach notice.
The company has taken immediate action to address the Roku data breach. Upon detecting the incident, the affected accounts were secured, and users were prompted to reset their passwords.
To provide further protection, the platform’s security team thoroughly investigated any unauthorized charges made by the hackers. They have taken steps to cancel relevant subscriptions and refund affected account holders.
Company Advises Users on Roku Data Breach
For legitimate account holders who were impacted by the breach, it is advised to visit the “my.roku.com” website. From there, click on the ‘Forgot password?’ option to receive a password reset link via email. This will allow users to regain control of their accounts and enhance their security.
Once you have regained access to your Roku account, it is recommended to navigate to the Roku dashboard and carefully review the recent activity, connected devices, and active subscriptions. This step will help ensure that all the account activity is legitimate and aligns with your usage.
It is important to note that Roku does not currently support two-factor authentication, which provides an additional layer of security even if your credentials are compromised.
While Roku takes measures to address security incidents and protect user accounts, it is advisable to regularly monitor your account and promptly report any suspicious activity to Roku’s customer support.
Roku Accounts Sold for Only 50 Cents
The 15000 compromised Roku accounts are being sold on stolen account marketplaces for as little as 50 cents.
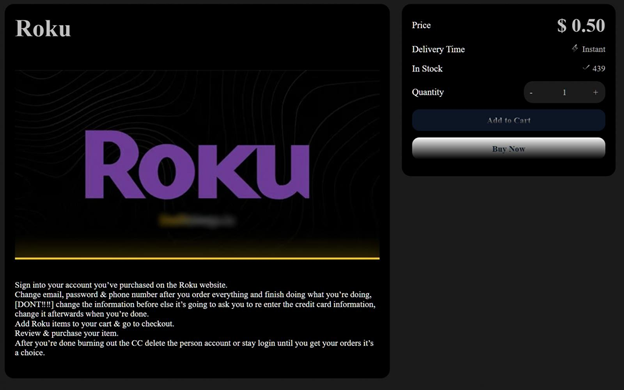
Source: BleepingComputer
These listings showcase a significant number of accounts available for purchase, with 439 accounts being offered at one instance.
The sellers of these accounts provide instructions on how to modify the account details to facilitate fraudulent purchases.
Buyers of these stolen accounts typically hijack them by replacing the account information with their own details.
They then utilize the stored credit card information to make unauthorized purchases, such as cameras, remotes, soundbars, light strips, and streaming boxes.
Once the fraudulent purchases are made, it is not uncommon for the perpetrators to share redacted screenshots of order confirmation emails on Telegram channels linked to the stolen account marketplaces. This serves as a form of proof of their successful transactions.
Hackers are Increasingly Using Credential Stuffing Attacks Against Popular Streaming Platforms
There have been reports of threat actors employing credential stuffing attacks using tools like Open Bullet 2 or SilverBullet.
These tools allow the importation of custom configurations, which are designed to carry out credential stuffing attacks against specific websites, including popular platforms like Netflix, Steam, Chick-fil-A, and Roku.
These threat actors have been utilizing a Roku configuration for several months to conduct credential stuffing attacks.
They have been able to bypass protections against brute force attacks and captchas by employing specific URLs and cycling through lists of proxy servers. This enables them to automate the process and increase their chances of success.