The LockBit ransomware group has acknowledged their involvement in the Capital Health attack that took place in November 2023. The adversaries are now issuing a warning, stating their intention to release the stolen data and negotiation chats.
Overview of the Capital Health Cyber Attack
What happened?
In late November, Capital Health discovered a cybersecurity incident affecting their systems. The IT team promptly responded by assessing the situation, protecting data, and restoring system functionality.
What did Capital Health do to address the situation?
The healthcare provider engaged law enforcement and third-party experts to assist in addressing the Capital Health data breach. The IT team implemented enhanced security measures, working tirelessly to recover and restore the affected systems.
What data has been exposed in the cyberattack on Capital Health? Is patient, employee, or financial data compromised?
Capital Health is currently working with a forensic investigation firm to assess the risk to patient and employee data. We will provide more information as soon as it is available.
Did Capital Health cybersecurity incident impact patient care?
All health care services are available at Capital Health and all systems have been restored.
Capital Health is Currently Investigating the Cyber Attack
Capital Health is a prominent healthcare service provider operating in New Jersey and parts of Pennsylvania.
The organization includes two major hospitals along with various satellite and specialty clinics. In November, Capital Health faced a significant disruption in its IT systems due to a cyberattack on its network.
As a result of the Capital Health attack, the organization was compelled to issue a warning that the incident would impact its operations for a minimum of one week.
Capital Health has posted a security incident notification on their website, stating that all systems have been successfully restored and operations have resumed without any issues.
Furthermore, they have implemented additional security measures to prevent the recurrence of similar cyber incidents in the future.
According to the latest updates from Capital Health, they are currently conducting an investigation to determine if any data was compromised during the cyberattack.
LockBit Claims Cyber Attack on Capital Health
The LockBit ransomware group has recently taken responsibility for the cyberattack on Capital Health. They have also included the healthcare company on their data leak extortion portal.
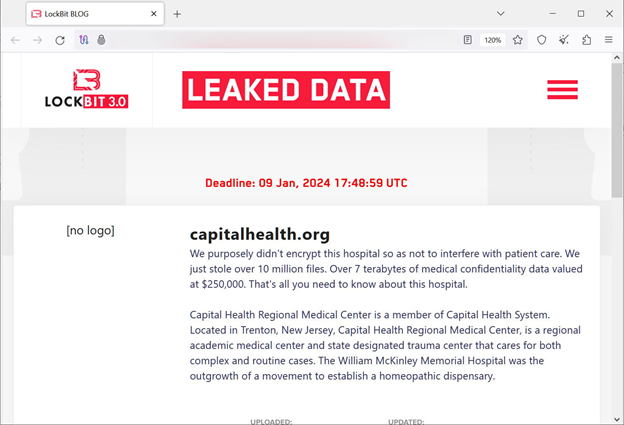
Additionally, the cybercriminals are claiming to have obtained seven terabytes of sensitive medical data in the Capital health Hospital cyberattack. They are threatening to release this data unless their ransom payment demands are met by the organization.
LockBit has a policy in place for its affiliates, stating that they should not encrypt files on hospital networks but rather focus on stealing data for extortion purposes.
However, it is worth noting that this policy has been violated multiple times by affiliates associated with the operation.
In the case of the attack on Capital Health, the LockBit operation claims that they deliberately chose not to encrypt the organization’s files. Instead, their focus was solely on stealing data.
“We purposely didn’t encrypt this hospital so as not to interfere with patient care. We just stole over 10 million files,”
LockBit ransomware commented on Capital health Hospital Cyber attack on their data leak site.
The LockBit operation has been involved in numerous cyberattacks targeting healthcare networks. Notable examples include the SickKids children’s cancer hospital, the Katholische Hospitalvereinigung Ostwestfalen (KHO) in Germany, and the Carthage Area Hospital and Claxton-Hepburn Medical Center in upstate New York.
LockBit Ransomware Raises Concerns in the Healthcare Industry for Repeated Cyber Attacks on Hospitals.
These incidents highlight the concerning trend of LockBit’s repeated targeting of healthcare organizations.
It is important to acknowledge that the LockBit operators have denied their involvement in the cyber attack on KHO. They claim that another ransomware gang utilized their leaked ransomware builder for the attack. However, these claims cannot be independently verified.
If cybercrime groups like LockBit and others persist in adopting a data-theft strategy, extorting hospital operators without causing direct damage to their infrastructure, it can create a misleading perception of these cyberattacks as relatively “harmless.”
However, it is crucial to recognize the potential consequences and risks associated with such incidents.
Even without encryption, ransomware attacks can have severe consequences. As part of the victim’s response to such attacks, system outages may occur, leading to disruptions in healthcare services.
Additionally, these attacks can result in catastrophic data breaches, compromising the personal and medical information of numerous individuals who received care at the targeted hospitals.
Furthermore, financially strained healthcare institutions may experience significant economic losses due to the impact of these attacks.
The healthcare sector has witnessed numerous high-impact ransomware attacks in recent times. Notable victims include Ardent Health Services, Integris Health, ESO Solutions, and the Fred Hutchinson Cancer Center (Fred Hutch).