Hewlett Packard Enterprise (HPE) is currently conducting an investigation into the HPE Data Breach that led to massive data theft. This comes after a threat actor reportedly posted stolen data on a hacking forum, claiming it includes HPE credentials and other sensitive information.
However, HPE has stated that they have not discovered any evidence of a security breach at this time. No ransom has been demanded. Nonetheless, HPE is taking the threat actor’s claims seriously and is actively investigating the situation. Further updates will be provided as the investigation progresses.
“We are aware of the claims and are investigating their veracity,”
“At this time we have not found evidence of an intrusion, nor any impact to HPE products or services. There has not been an extortion attempt.”
HPE’s Sr. Director for Global Communications Adam R. Bauer told BleepingComputer on Thursday.
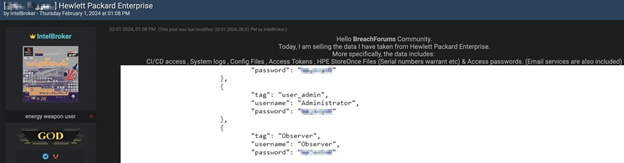
The threat actor known as IntelBroker, who is selling the alleged HPE data, has shared screenshots of what they claim to be stolen HPE credentials. However, they have not revealed the source of the information or the method through which it was obtained.
The investigation into the validity and origin of the data is still ongoing. Updates will be provided as more information becomes available.
“Today, I am selling the data I have taken from Hewlett Packard Enterprise,”
“More specifically, the data includes: CI/CD access , System logs , Config Files , Access Tokens , HPE StoreOnce Files (Serial numbers warrant etc) & Access passwords. (Email services are also included).”
The threat actor says in a post on the hacking forum.
HPE Data Breach Update
However, in an update, the company said that the data being offered for sale online was obtained from a “test environment.”
“Based on our investigation so far, the data at issue appears to be related to information that was contained in a test environment. There is no indication these claims relate to any compromise of HPE production environments or customer information,”
Bauer said in a statement.
HPE Investigates Data Breach Where Russian Hackers Breach HPE Corporate Email Accounts
This investigation follows HPE’s recent disclosure that their Microsoft Office 365 email environment was breached in May 2023. The company believes the hackers responsible were associated with the Russian APT29 hacking group, which is linked to Russia’s Foreign Intelligence Service (SVR).
During the breach, the Russian hackers gained unauthorized access to HPE’s cloud infrastructure and stole SharePoint files and data from various departments, including the cybersecurity team. HPE was alerted to the breach again in December when their cloud-based email environment was compromised once more.
“On December 12, 2023, HPE was notified that a suspected nation-state actor had gained unauthorized access to the company’s Office 365 email environment. HPE immediately activated cyber response protocols to begin an investigation, remediate the incident, and eradicate the activity,”
HPE said in a statement to the BleepingComputer.
“The Company, with assistance from external cybersecurity experts, immediately activated our response process to investigate, contain, and remediate the incident, eradicating the activity.”
reads FORM8-K
Indeed, just prior to HPE’s disclosure of the Russian hack, Microsoft also experienced a similar breach. APT29 targeted several corporate email accounts belonging to Microsoft’s leadership team, as well as employees in the cybersecurity and legal departments.
Microsoft later revealed that the threat actors gained access to these accounts by exploiting a misconfigured test tenant account through a “password spraying” attack.
Furthermore, HPE faced a breach in 2018 when APT10, a Chinese hacking group, infiltrated IBM’s networks and leveraged that access to compromise devices belonging to IBM’s customers.
HPE also disclosed in 2021 that data repositories of its Aruba Central network monitoring platform were compromised. This breach allowed attackers to gain unauthorized access to data related to monitored devices and their locations.